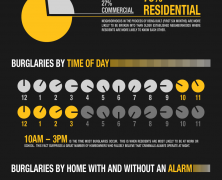
To make the ultimate burglarproof home is almost impossible. Burglars will always use advanced technologies that can break even the most sophisticated security systems. However, CCTV can thwart them from plundering you property.
Know Your Enemies Online
visualized by: Trend Micro
Knowing who your friends are from your enemies online is your best defense against the online threats. A holistic overview of the various network threats and their names.
TSA Effectiveness
visualized by: OnlineCriminalJusticeDegree.com
A documented dispute between the TSA funding boosters and the itching doubters who are questioning the competency of that sheme.
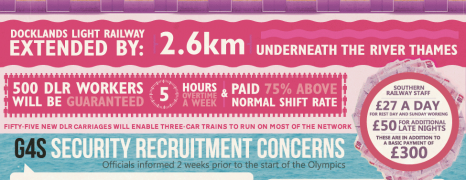
The Impact Of Olympics
visualized by: ClickSoftware
What are the resources needed to run a super Olympiad? What are the critical points and the extent of activity that should be considered by the hosting country on managing such a glorious event? Read the numbers that refer to 4 latest Olympic games.
Android Malicious Apps
visualized by: Trend Micro
Trend Micro – the leading web security company published this report to pose a worry among mobile users about the usage of personal data stored and collected by sneaky Android apps.
Social Oversharing and Security
visualized by: Quin Street
Have you ever wondered if we are overdoing it with social sharing? Security issues might come up when you thoughtlessly update your status. After all, oversharing is strongly related with emotional disorders.
Keep some things private and know if you are suffering from FOMO – the social media syndrom of our days.
Facebook Reporting G...
visualized by: Facebook
Facebook manifests for the safety and security of users and rolls out this native chart to show us the competence of its spam/ abuse report system and the tools we have in our hands.
Corporate Networks At Risk
visualized by: SoftChoice
A lack of process around corporate networks device management is exposing them to critical risk, high maintenance costs and performance degrading. See the current state of network maintenance and security concern from organizations.
Small Business Cyber Security
visualized by: VERACODE
Small business owners consider their property like needle in haystack for the aspiring hacker. Unfortunately cyber security proves to be conversely proportional to the business volume.
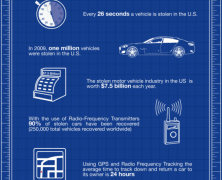
Theft Proof Car
visualized by: Home Security
Are you into investing time and money in creating the ultimate theft-proof car? Find here the best automobile security devices together with some smart tips.
Linkedin Passwords L...
visualized by: Rapid 5
Bad passwords make bad passphrases and cracking algorithms have been accordingly set up for these cases. 6.46 million stolen Linkedin passwords
Web Applications Security Cheat Sheet
visualized by: VERACODE
Data breach could cost you a fortune compared to investment in integrated security scheme as a precaution measure. Find top keynotes for building secure web applications
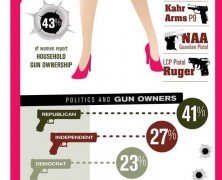
Girls and Guns
visualized by: Doctor Who?
When girls go wild. Watch out for the hit-wo-man! Increasing gun ownership by women.
Can We Trust Google?
visualized by: Background Check
Trust NOONE! A lot of changes have been implempented to the Google applications lately showing a change in the philosophy. User data collection and privacy involved are issues that arousing great concern lately,
Top 7 IT Certificati...
visualized by: Phoenix TS
Are you thinking of a career shift to secure your professional life future? IT might be the solution. Check here average salary by certification completion, experience and job title.
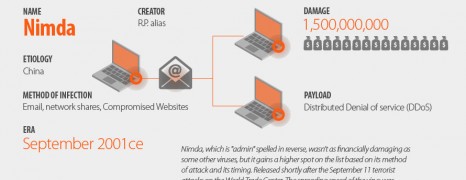
The Greatest Human And Digital Viruses
visualized by: Uniblue
They are threatening, sometimes lethal and always intrusive and destructive. Get your antibiotic before clicking!