American internet is of the most dashing worldwide. American Internet services give us some surprising statistics about the the state and volume of cyber security data breach across the US starting from 2005 and up to 2013.
eGov Security
visualized by: Symantec
Egov implementation is expanding year by year in developed countries. The question is how public sector’s IT departments can stem the increasing threat of cyber attacks, avoid the pain of data breach and defend their system’s security?
Password Weakness
visualized by: BackgroundCheck.org
Internet has gone wild and according to experts, even the strongest password can be cracked depending on the time and effort a skilled hacker would put on. This report highlights the common password weaknesses and hacking methods and suggests some best practices to protect your online information until the coming of new age in authentication methods.
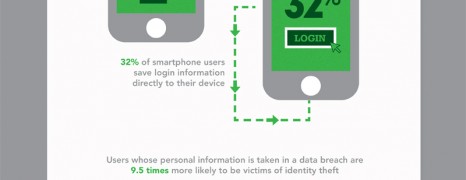
Mobile Security Awareness
visualized by: Security Coverage
January 28th has been named as Data Privacy Date. This spot brings mobile security awareness on the spotlight, by presenting notable facts from the currenst state in the mobile world followed by some essential tips on keeping your device the least vulnerable to security breaches.
IT Security Breaches
visualized by: Dell
Nowadays more companies are being proactive about data protection. There are a number of tools to fight against loss of data security. But more challenging is increasing data protection in malicious attacks coming from inside and outside the organization. Network security is becomig most important aspect in IT industries.
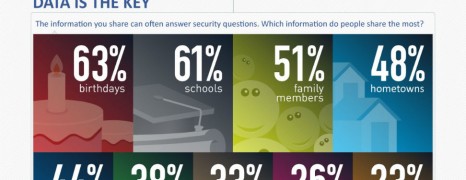
Social Networks Privacy Risks
visualized by: Trend Micro
Trend Micro awakes us with an overview on the type of information we publicly share on social networks and the risks involved. Everything you post can and will be used against you!
Password Theft Statistics 2012
visualized by: Security Coverage
Passwords dominate our daily life as they have evolved to key-controllers of our major activities and transactions. But how safe do you feel about your personal information against cybercrime in 2012?
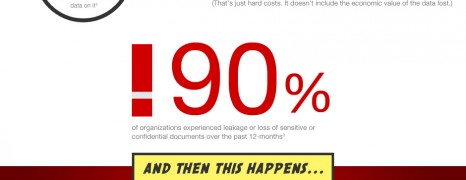
File Sharing and Security
visualized by: IglooSoftware.com
Business users are demanding flexibility in data and information usage by utilizing cloud services. However IT people and businesses are vastly itching for confidentiality issues. Could these two forces be harmonically combined?
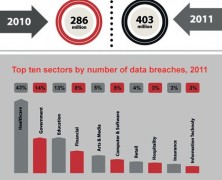
Cybercrime in Busine...
visualized by: BlowFish Digital
Cybercrime is the 2nd most reported economic crime against the financial services industry. Read some numbers that may make you reconsider your security infrastracture.
Small Business Cyber Security
visualized by: VERACODE
Small business owners consider their property like needle in haystack for the aspiring hacker. Unfortunately cyber security proves to be conversely proportional to the business volume.